- + 43 1 869 96 09
- + 49 30 346 490 58 0
- office@edv-n.com
- Kolbegasse 69, 1230 Vienna
- Bundesallee 213-214, 10719 Berlin


Through our solutions, we ensure that:
This is achieved through our Zero Trust-based security solution. This fundamentally trusts no program and no communication. With every computer and program start and with every communication setup, the corresponding process is checked. An AI decides immediately and independently whether a process can be trusted at the current execution time or not.
Additionally, by allowing you to trace the communication across your entire network up to one year back, it is also ensured that all communication processes are traceable and any unwanted communication, even from the past, can be detected and tracked.

Low impact on your
IT infrastructure with
our solution.
Every program and every
communication process is
always re-evaluated with each execution.
of anomalies
in the network.
No questions to the user
about whether they want to allow or block something,
the AI decides independently.
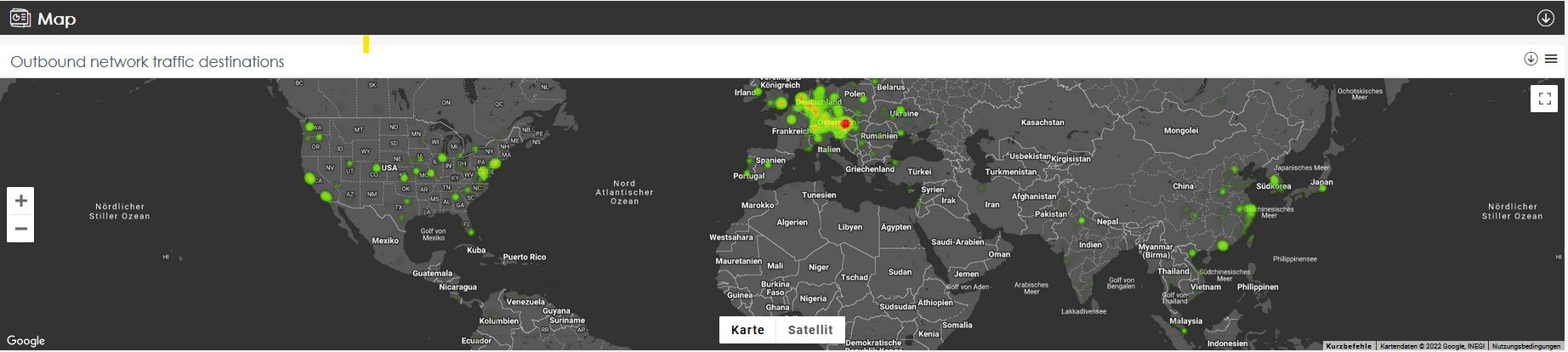
We see to which endpoints your systems connect all over the world. This allows us to track them, often even down to the street corner where they are located.
With the help of the integrated Threat Hunting Service, we can also see potential vulnerabilities in your IT landscape and identify them before they become an entry point.

Should personal data be unstructured or unauthorized on your systems, they can be searched for, identified, and removed if necessary.
This also supports you, for example, with GDPR inquiries, as it enables you to always provide information about which data you have stored from a specific person, even without specialized software.
A significant number of unauthorized accesses to company data do not occur through an external attack, but internally, within the secured system. Our software therefore detects whether and where data is being extracted and forwarded from your system.
